Codes and Ciphers of the Civil War
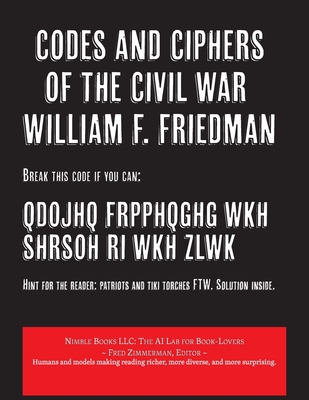
Codes and Ciphers of the Civil War
QDOJHQ FRPPHQGHG WKH SHRSOH RI WKH ZLWK
Hint for the reader: patriots and tiki torches FTW. Solution inside.
This famous lecture by William F. Friedman, the father of American cryptography, provides a fascinating glimpse into the world of cryptology during the American Civil War, examining the systems used by both Union and Confederate forces. Key Points: Albert J. Myer and the Signal Corps: The lecture details Myer's development of the "wig-wag" system of visual signaling and the subsequent establishment of the Signal Corps. The initial lack of electrical telegraphy capabilities and the ensuing rivalry with the U.S. Military Telegraph Corps (USMTC) created significant challenges for the Signal Corps. Union Cryptosystems: The lecture describes the two primary cryptosystems used by the Union: Myer's Cipher Disk: Employed by the Signal Corps for tactical communications, this disk allowed for changing the visual signal equivalents for letters, offering a basic level of encryption. Route Ciphers: Utilized by the USMTC for strategic communications, these ciphers involved transposing words within a matrix, offering a more complex level of encryption compared to the Myer disk. Confederate Cryptosystems: The lecture explains the Confederate reliance on the Vigenère cipher, also known as the "court cipher," for both tactical and strategic communications. This system used a keyword to shift alphabets cyclically, providing a polyalphabetic encryption method. Weaknesses of the Systems: The lecture critically examines the weaknesses of both Union and Confederate cryptosystems: Myer's Cipher Disk: Susceptible to cryptanalysis due to its monoalphabetic nature. Route Ciphers: Vulnerable if codebooks were captured, and the limited number of code words reduced their effectiveness. Confederate Vigenère Ciphers: Leaving words unenciphered and revealing word lengths through the cipher text compromised security. Additionally, the limited number of keys used during the war made them susceptible to cryptanalysis. Additional Observations: The lecture highlights the importance of cryptology in warfare, emphasizing its role in secure communication and the impact of insecure communications on the outcome of battles and campaigns. It reveals the lack of advanced cryptographic knowledge during the Civil War era, with both sides relying on relatively simple systems that were often vulnerable to cryptanalysis. The lecture raises interesting questions about
PRP: 123.59 Lei
Acesta este Pretul Recomandat de Producator. Pretul de vanzare al produsului este afisat mai jos.
111.23Lei
111.23Lei
123.59 LeiLivrare in 2-4 saptamani
Descrierea produsului
QDOJHQ FRPPHQGHG WKH SHRSOH RI WKH ZLWK
Hint for the reader: patriots and tiki torches FTW. Solution inside.
This famous lecture by William F. Friedman, the father of American cryptography, provides a fascinating glimpse into the world of cryptology during the American Civil War, examining the systems used by both Union and Confederate forces. Key Points: Albert J. Myer and the Signal Corps: The lecture details Myer's development of the "wig-wag" system of visual signaling and the subsequent establishment of the Signal Corps. The initial lack of electrical telegraphy capabilities and the ensuing rivalry with the U.S. Military Telegraph Corps (USMTC) created significant challenges for the Signal Corps. Union Cryptosystems: The lecture describes the two primary cryptosystems used by the Union: Myer's Cipher Disk: Employed by the Signal Corps for tactical communications, this disk allowed for changing the visual signal equivalents for letters, offering a basic level of encryption. Route Ciphers: Utilized by the USMTC for strategic communications, these ciphers involved transposing words within a matrix, offering a more complex level of encryption compared to the Myer disk. Confederate Cryptosystems: The lecture explains the Confederate reliance on the Vigenère cipher, also known as the "court cipher," for both tactical and strategic communications. This system used a keyword to shift alphabets cyclically, providing a polyalphabetic encryption method. Weaknesses of the Systems: The lecture critically examines the weaknesses of both Union and Confederate cryptosystems: Myer's Cipher Disk: Susceptible to cryptanalysis due to its monoalphabetic nature. Route Ciphers: Vulnerable if codebooks were captured, and the limited number of code words reduced their effectiveness. Confederate Vigenère Ciphers: Leaving words unenciphered and revealing word lengths through the cipher text compromised security. Additionally, the limited number of keys used during the war made them susceptible to cryptanalysis. Additional Observations: The lecture highlights the importance of cryptology in warfare, emphasizing its role in secure communication and the impact of insecure communications on the outcome of battles and campaigns. It reveals the lack of advanced cryptographic knowledge during the Civil War era, with both sides relying on relatively simple systems that were often vulnerable to cryptanalysis. The lecture raises interesting questions about
Detaliile produsului